For years, immigration enforcement agencies have been using invasive cell phone surveillance technology known as Stingrays in near-total secrecy. To find out more, the ACLU and New York Civil Liberties Union filed a lawsuit under the Freedom of Information Act, and now we’ve forced the agencies to turn over documents revealing new details about the agencies’ practices. Today, we are publishing more than a thousand pages of record we’ve received from U.S. Immigration and Customs Enforcement (ICE) about their purchase and use of Stingray technology. The documents reveal some significant gaps in public knowledge about the agency’s practices and raise significant privacy concerns.
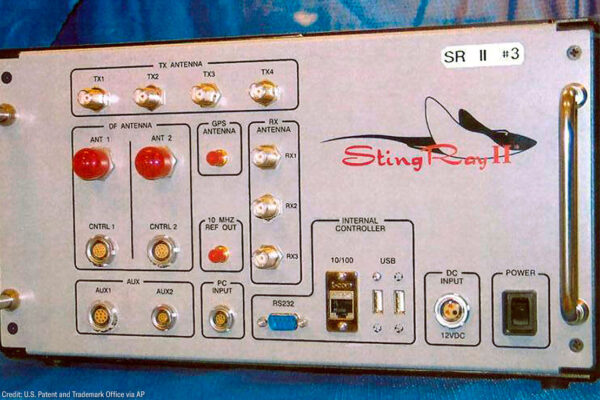
Stingrays, also known as cell site simulators or IMSI catchers, track and locate cell phones. The devices mimic cell phone towers by sending out signals that trick cell phones in the area into transmitting their unique identifying information, ensnaring not only a target’s cell phone but also those of nearby bystanders. Using those transmissions, government agents can precisely locate phones, and can learn the identities of all phones in a particular area.
We initially submitted a FOIA request to ICE and Customs and Border Protection (CBP) in 2017, after the Detroit News reported on a case where ICE used a cell site simulator to locate and arrest an individual on immigration-related charges. That request was met with two years of near silence from the agencies, so last December we filed a lawsuit asking a federal court to order ICE and CBP to produce a range of records about their use, purchase, and oversight of the technology. ICE has since handed over more than a thousand pages of documents. CBP, on the other hand, maintains that it can’t find a single page dealing with cell site simulators, despite public evidence that the agency has spent millions on them. On Friday, we filed a motion asking the court to compel CBP to live up to its legal obligations regarding transparency under the FOIA.
There’s good reason to demand transparency from these agencies. Through the documents we received from ICE alone, here’s what we’ve learned:
- ICE upgraded their cell site simulator devices from the Harris Corporation’s Stingray II to a new model called Crossbow. Prior to release of these records, the existence of the Crossbow model was not publicly known. As of January 2020, ICE was still using Crossbows. Although records obtained through FOIA and other litigation in recent years has revealed some information about the costs and capabilities of the Stingray and other models of cell site simulators, we don’t know what the Crossbow can do, or whether it raises different concerns than other versions of the technology.
- In September 2017, ICE said it had used cell site simulators 223 times, including 95 times to “apprehend” people and 104 times to “gather evidence relevant to a case against any apprehended individual.” From Jan. 1, 2019 to Oct. 7, 2019, ICE deployed cell site simulators 134 times, which located at least 80 people and resulted in 22 arrests. Fifty-one pages of weekly reports chart ICE’s use of this technology over time. From the piecemeal reported totals we received in sets of documents dated from 2017 to 2019, we can surmise that ICE used cell site simulators at least 466 times. These figures supplement data previously reported by Buzzfeed News showing that from Jan. 1, 2013 to Oct. 11, 2017, Homeland Security Investigations, a branch of ICE, used cell site simulators 1,885 times.
- For all of law enforcement officials’ talk about the need to maintain secrecy around law enforcement use of cell site simulators, a presentation by DHS’s National Cybersecurity & Communications Integration Center acknowledges that “hackers” and others can also obtain access to cellular communications data using Stingrays, and discusses a pilot program to deploy sensors to detect this technology in the National Capitol Region. The presentation reveals that in 2016, DHS “Detected likely IMSI catcher monitoring/tracking phones.” This document suggests that excessive government secrecy about cell site simulators may be self-defeating, by failing to alert American cell phone users about threats to the privacy and security of their communications.
- Although DHS and ICE acknowledge that cell site simulators can interfere with cell phone calls in the area, the documents reveal that “Neither ICE nor USSS (United States Secret Service) has funded independent interference testing.” The FBI has similarly stated that it “does not test or measure the interference levels” of its cell site simulators. This stands in contrast to federal police in Canada, whose tests revealed that cell site simulators could interfere with more than 50 percent of 911 calls, leading the agency to mandate limitations on use of the technology. Senator Ron Wyden has repeatedly raised this problem with federal law enforcement agencies, but unless something has changed since the dates of these documents, DHS and the FBI don’t seem to be taking it seriously.
- DHS requires all of its components that use cell site simulators, including ICE and CBP, to implement policies governing use of the technology. ICE’s policy governing the use of the technology is now public for the first time. According to the policy, ICE recognizes that it normally needs to get a search warrant before using a cell site simulator, except when there are “exigent circumstances.” But it is unclear if ICE regards this as the only exception to the warrant requirement, as both DHS’s policy and ICE training materials also say “exceptional circumstances” can justify bypassing the warrant requirement. The manner in which ICE has defined both “exigent” and “exceptional” circumstances in the training materials provides law enforcement officers with little guidance as to what these terms mean or when the agency considers them properly invoked. This is concerning because it raises the prospect that agents may be short-circuiting the need for judicial oversight when in circumstances where there is no true emergency.
There can’t be accountability without transparency. The release of these records — albeit with redactions — provides some helpful insights into what was previously an extremely secretive surveillance practice. For example, the documents provide multiple assertions that ICE and CBP are not using cell site simulators in civil immigration investigations.
That’s good news, but concerns remain. We know that despite claiming not to use Stingrays for civil immigration enforcement, ICE does use the technology in its ever-expanding category of “criminal” immigration investigations, including arrests for the crimes of illegal entry and reentry. And although the requirement to get a warrant is positive, we still don’t know what the agency believes qualifies as an “exigent” or “exceptional” circumstance that lets agents avoid the warrant requirement. Those are just a few of the outstanding questions.
We also continue to know virtually nothing about CBP’s use of this technology. CBP has stated that it searched for records three times in response to our FOIA request and has not identified a single responsive record. But the agency’s no-records response is impossible to square with publicly available information as well as the documents we received from ICE. A 2016 Congressional Report reveals that as of four years ago, CBP had spent $2.5 million to purchase 33 cell site simulator devices. And, in 2017 letters to Sens. Ron Wyden and Al Franken (redacted versions of which were provided to us for the first time in this case), DHS stated that CBP has used cell site simulators and was in the process of drafting a policy to govern their use.
We’re demanding the court order CBP to explain how it conducted its prior searches for records responsive to our FOIA request and to conduct a new search for responsive records.
The use of powerful, surreptitious surveillance equipment is concerning in any context. But when agencies such as ICE and CBP, with a long history of abusive practices, evade requests for information and then obfuscate provided information, we should all be concerned.
Alexia Ramirez, Fellow, ACLU Speech, Privacy, and Technology Project